Sharkfest 2017 US Recap – 10 years of Sharkfest!
Time always flies at Sharkfest, the annual Wireshark conference, and the 2017 edition – being the 10th Sharkfest in the US – has been no exception. On Friday Sake and me talked about how fast the 3 day conference had felt and we both agreed that “hm, it seems just to have started moments ago and it’s already time to go back home”. I don’t know about you, but for me and him that’s a sure sign of a good conference. Not a single boring moment.
Carnegie Mellon
Sharkfest 2017 US was the first Wireshark US conference that took place on the east coast, so I was curious how that would turn out. Carnegie Mellon University (CMU) in Pittsburgh was chosen as the place for us to gather around to geek out about Wireshark, packet capture, network analysis and network forensics.
From my point of view CMU was a good location, bringing back the “campus feeling” that Stanford, Berkeley and San Rafael had in the past. The weather was certainly very different – it was raining a lot, and many people had trouble traveling to Pittsburgh, including me and Landi. Our last leg from Washington to Pittsburgh was canceled due to bad weather (while it was sunny and hot in Washington), so we decided to pick up our luggage and drive instead. We got to Pittsburgh in a little over 4 hours, and on the way we found the bad weather with heavy rain like I had only seen in Florida before: “Oh. That bad weather. Got it.”
Don’t drink and dive into packets…
The campus rules of CMU concerning the consummation consumption of alcoholic beverages during Sharkfest felt a bit odd. There was some sort of “low level prohibition” going on, with a team of campus police guarding over a rule of “2 alcoholic drinks per hour per person”. Which apparently was something the awesome organization team run by Janice and Laura only learned about minutes before the welcome reception started, handing out drink vouchers:
Anyway, we had fun nonetheless (who needs that much alcohol, anyway? 🙂 ), and the restrictions didn’t really have any kind of negative effect as far as I can tell. And of course there was enough beer available in the hotel – Simon, Sake and me enjoyed a bottle of “Landshark” beer after Betty had mentioned it:
Other than that, the location was good, carrying that usual spirit of creativity and learning that universities in the US do so well (compared to some I’ve seen in Germany, but maybe that’s just me).
I have to say that the Computer History Museum (Sharkfest 2015 and Sharkfest 2016) in Mountain View had an advantage that became apparent to some of us who had been there the last two years: the conference in the museum felt more “compact”. There, you left a presentation and almost automatically walked back into the area with the Shark Reef, the Developer Den and the dining tables, and you met the other attendees. At Carnegie Mellon, everything was more spread out, and you had to walk to different places for the talks, so people didn’t gather as much. The same had been the case with San Rafael in 2014 and Berkeley in the two years before that.
Developer Den
The “Developer Den” is the place where the Wireshark core developers lurk and hack new stuff into the Wireshark code base. Well, those who traveled to Sharkfest, and sometimes there’s new faces and sometimes developers had been there before couldn’t be there this year. I particularly missed Alexis, Jim, Dario and Bálint – do me a favor and be there again next time, you hear me? 😉
This year seemed to be a bit different than previous years – there were a lot more attendees daring to enter the room and actually talk to the developers about bugs, feature requests and general development topics. So that was a great success – I think I have never taken a picture in the developer den were the RAD-factor (Ratio of Attendee/Developer) was 1:1 as seen in that picture above. Graham, Peter, Michael and Anders all discussing something with a Wireshark user is awesome. Also, this shows Landi and Peter finding out that the Wireshark TCP expert code only seems to be able to detect RTO-based and Fast Retransmissions, and doesn’t know what SACK edges means in an ACK packet. Can you believe it? It never occurred to me either, so I never checked…
Oh, almost forgot: Peter also brought Wireshark stickers! 😀
My Sessions
I presented four sessions this year, with a total of 6 time slots, with two sessions running as double slots. Which turned out a little more stressful than expected, not only because Hansang‘s flight from New York was canceled as well due to the bad weather situation – so on Monday I agreed to swap his Tuesday morning slots with my Thursday afternoon TraceWrangler slots. The problem was – I hadn’t prepared anything up to that point (what else is new…), which meant did get a lot less sleep that night than expected… But it went fine I think.
The second session was TCP hands-on (the only session not being in the main room, and that means there is no video) and I had shared the files two weeks before the conference here and on the Sharkfest USB sticks. My audience surprised me when only 2 or 3 people had actually looked at the files before the session, so my “Lessons Learned” for that kind of session is to expect nobody having done their “homework” 🙂
The third session was a double slot presentation with Landi, talking about analyzing performance problems with multiple capture points. We had done a similar talk in Berkeley a couple of years ago in a single slot, but I think having twice as much time this year was a good thing.
The fourth session was a special one called “The Doctor is In! Packet Trace Reviews with the Experts”, with four presenters on stage in the main room: Hansang, Sake, Landi and me (I took the picture, that’s why there’s only three):
We got a couple of capture files from the audience and went through them live and unprepared, so that everyone could watch us work our way through the problem. Most of them were related to some kind of “slow transfer” problem description, and in one case we diagnosed a 100Mbit/s bandwidth limit as the most likely cause – as far as I heard that problem was later confirmed and resolved as a license issue. I think the most interesting part of it for the audience was that all four of us had more or less different ways to work through a trace file. Also, we scroll packets whenever we want! 😀
Sessions I attended
I didn’t have much time to join sessions of other presenters, which was one of the effects of having so many slots myself (which I will reduce next time, as really felt it was too much). I saw Hansang’s and Chris Greer‘s talks, but I skipped a few others in the big room because I knew I could watch them later on the Sharkfest Youtube channel. I have already watched the ones by Endace’s Stephen Donnelly and Riverbed’s Kary Rodgers, and I have to say I like the new split screen look (way to go, Angelo!). The sound is still a bit hard to understand sometimes, but I think that can’t be helped unless tapping into the microphone feeds, which is hard to do if it’s not your own gear.
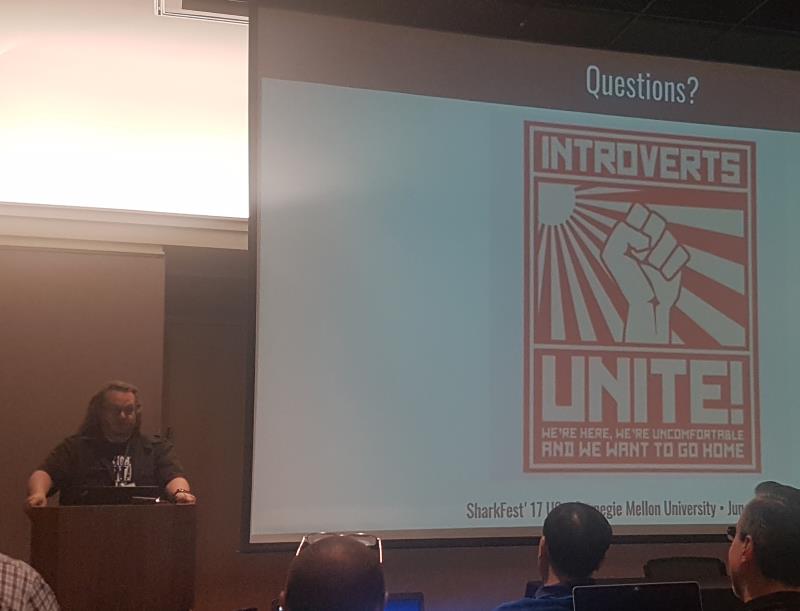
The ones I really wanted to see was Mike Kershaw’s “Network Security… Haven’t We Solved It Yet?”, because Landi had seen it a year ago and really liked it. It was awesome (incredible slide clicking speed for some topics), and I had to laugh at his final slide:
The other security related talk I wanted to see was Brad Duncan’s “Analyzing Exploit Kit Traffic with Wireshark”, since I loved his malware traffic analysis web site with lots of exercises and examples. It was interesting to see how someone else does investigations into malicious traffic, and I also found some time to talk to Brad afterwards.
Events
There were two events this year that were noteworthy: Sake’s esPCAPe challenge, an escape room game based on a pcap (of course!), and Shark Bytes.
The esPCAPe Challenge
Sake spent a lot of time and energy on building a fun challenge during one of the evening dinner receptions. Each table would work on the PCAP files as a team, trying to find all the hidden things he had put there. He even had a web page that showed the current status:
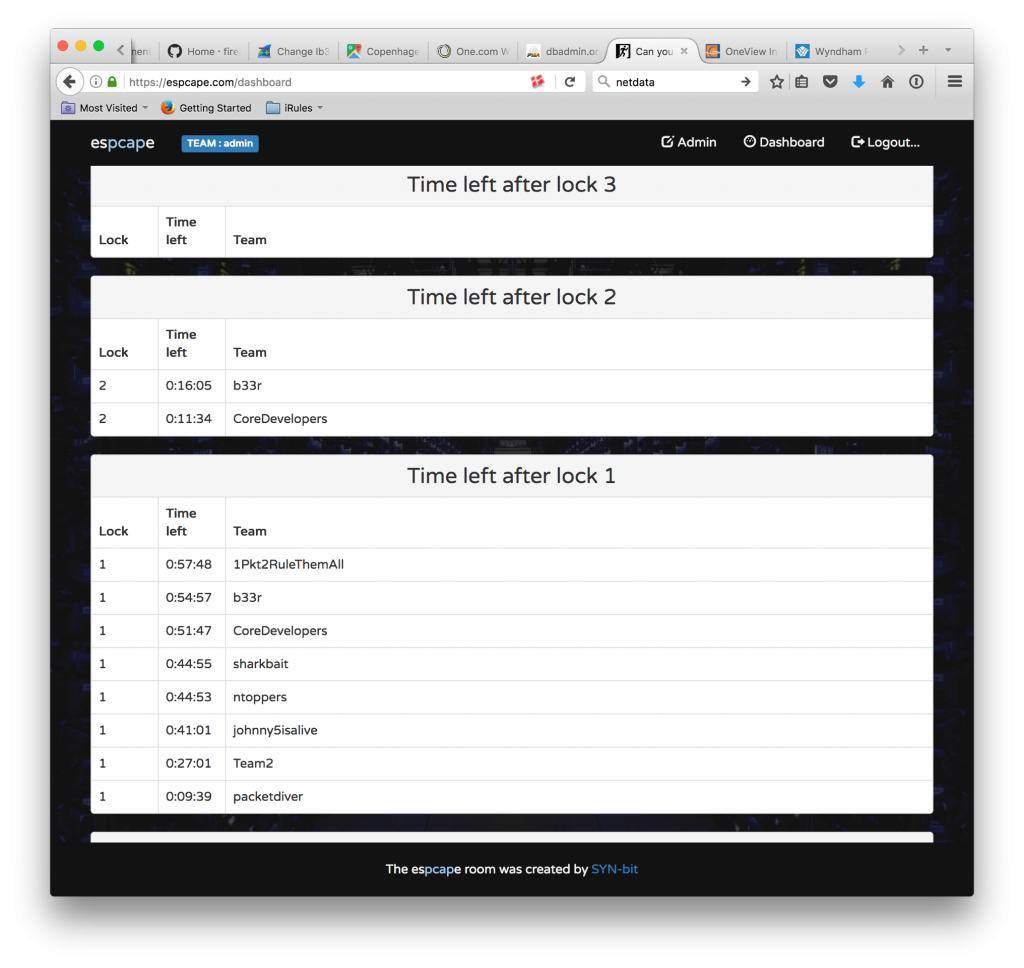 Team “b33r” won in the end (gratz!), with no team being able to break lock number 3. My team (“johnny5isalive”) got stuck at a specific point (very very annoying; I still got no clue why), and time ran out. And before any of you ask: I won’t tell you more about the details of the challenge here for a simple reason: we might see it at again, so no trace files and no spoilers! 😉 From my point of view it’s totally up to Sake of where and when he wants to release a solution.
Team “b33r” won in the end (gratz!), with no team being able to break lock number 3. My team (“johnny5isalive”) got stuck at a specific point (very very annoying; I still got no clue why), and time ran out. And before any of you ask: I won’t tell you more about the details of the challenge here for a simple reason: we might see it at again, so no trace files and no spoilers! 😉 From my point of view it’s totally up to Sake of where and when he wants to release a solution.
Shark Bytes
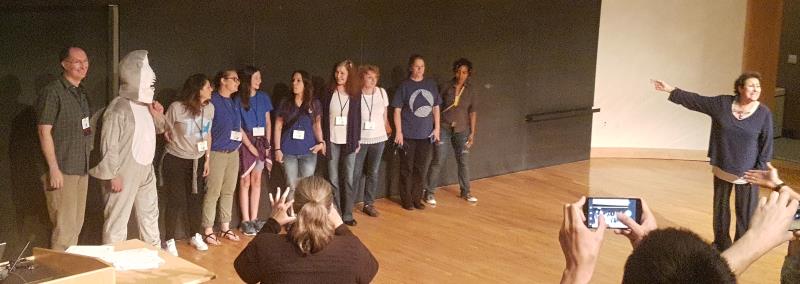
Shark Bytes is a session that runs in a keynote slot almost every year now, with multiple 5 minutes presentations unrelated to packet analysis. Think of it like short TED presentations about various topics, some fun, some inspirational, some energetic on an almost nuclear level (whenever Megumi-san is presenting :-))
As always, Shark Bytes are highly recommended, and they 2017 US Shark Bytes should turn up at the Sharkfest YouTube channel at some point in time.
Acknowledgements
Sharkfest is an amazing conference, but it wouldn’t be possible without the hard work of the team behind the scenes:
Thanks so much for all the hard work!
Then there’s Sake who build the esPCAPe room challenge – kudos for that as well! Also, thanks to the brother of Janice who created all the wonderful cakes! And of course all the vendors that make the conference possible with their support!
Oh, and thanks to Betty who got me these awesome shark cufflinks (for those very rare occasions when I have to present in suit & tie):
That’s what Sharkfest is: a friendly, open community that loves to help, teach and learn from each other. So if you have anything to do with packet analysis you should be there next time 😉








Nice piece.
Nice summary of the conference Jasper. Thank you.
Great write up! I have more fun at our family reunion every year. See you in Portugal.
Thanks, Betty! See you in Portugal!
Very well written and a good read. Thanks for the insights.
Thank you Phil! Hope you can make it to one of the next ones maybe? 🙂
Nice review write up. This was my first Sharkfest and as a Wireshark rookie I found it very informative. I’ll be going through my notes and the presentations on the retrospective page for things I can share with my co-workers.
Thanks, Greg, glad you liked it 🙂
Wee bit of a nitpick: Note that “consumption” of something is hugely different from “consummation” of something. When someone “consummates” an event (usually), one “completes” it. In the case of a marriage, it means you finally had sex as spouses. I don’t think you want to intimate you were having sex with your beer bottle(s). ;-P
Gotcha. Fixed it 🙂