Sharkfest 2016 recap
Another Sharkfest has come and gone, and once again it has been a great conference. If you’re into packet analysis, network forensics or network troubleshooting there is no other event that has the same density of information. It’s really a “specialist” conference, in a very open and friendly way, and newcomers are always welcome.
One of the amazing things happening at Sharkfest every year is that speakers stay to sit in talks of other speakers. In my experience that doesn’t happen as much (or at all) at other conferences – and even when it happens, it isn’t like Sharkfest. I sat in Werner’s Layer 2 talk with Hansang next to me, and Werner later told me later that that was quite intimidating at first. I totally understand that, but at Sharkfest, having a skilled person listen to your talk shouldn’t intimidate you – it just means that the topic is interesting, and there’s always something new to be learned. My own personal goal is that everyone sitting in any of my talks leaves it having learned something new in the end, no matter how small.
The other great thing at Sharkfest is that you can also talk to experienced network analysts and have them help you with questions or problems you’re facing in your capture files:
It’s a conference set up to help people improve their skills in any way possible, and I saw Laura do a new thing this year that attendees liked a lot: Lunch & Learn (I honestly can’t remember what it was called, but she was presenting Wireshark tips & tricks in the Reef while attendees had lunch).
Talk, Talk, Talk
This year I turned in two talks, one about IoC verification (you can read about it here, too), and an updated version of my 2013 “Top 5 False Positives” talk. At some point last year Janice (the one and only “Mama of Sharkfest“) asked if I could do more than those two, so I agreed to another talk spanning two slots (a total running time of 2:30 hours). This was a first for me, and my main problem was that I had no experience with that amount of time – I know how to work with almost any duration up to 75 Minutes (usually exceeding the time, but that’s something I share with a lot of other speakers). I hoped I had enough interesting material (as far as I can tell, all there is no such thing as a speaker not being worried about that), but in the end it turned out to be fine. Landi always says I can talk for an hour with just one slide anyway, and he’s probably right.
Having twice the time was nice, and so I “tortured” my audience with a slide deck first before going into demo mode: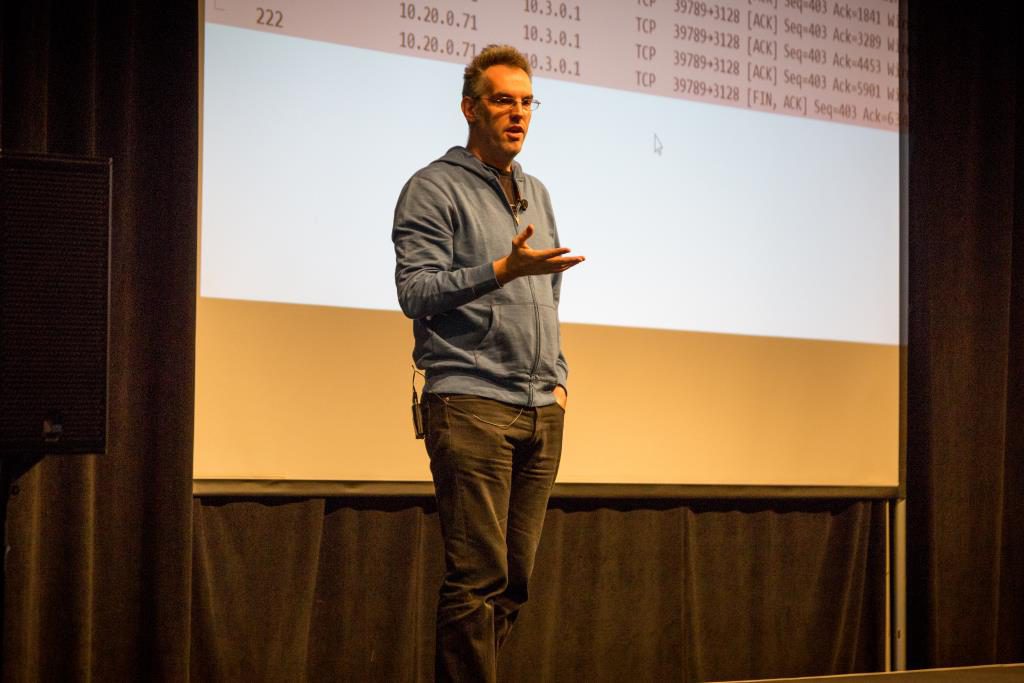
The only thing that was slightly annoying was that the stage was illuminated from above, but it was required for the video recording so I couldn’t have it turned off. It also makes all the black stuff shine in a yellowish gray on the pictures. By the way, the video recordings should be up on retrospective page by now, but as far as I know only the sessions in the Auditorium were filmed (there were 2 other rooms that weren’t). Funny story: I had multiple conference attendees apologizing to me for not being in my talk, because “they can watch it online later and go see something else in real life” 🙂
I had the chance to see Hansang do his talks, which is always interesting since he’s got even more experience doing network analysis than I have. By the way, it was a great thing to have 3 projectors in the main hall this year, at full HD resolution – it was so annoying last year having only one with 1024 x 768 (if you ever tried demoing packet stuff with Wireshark on a resolution like that you’ll know what I mean):
Landi was also busy with a few talks, doing his tshark magic to process capture files and extract information fast:
At the same time, the Wireshark core developers were talking about the best way to keep improving your favorite network analyzing tool:
Location, location, location
The location was once again the Computer History Museum in Mountain View, and even though that it was a cool venue I still miss the university locations of previous Sharkfests. They had a very special vibe that seems to be unique, and even though I know they are a pain for the Sharkfest team to deal with (universities are not really experienced in running conferences, so it’s much more work to organize an event there) I hope we’ll go back to one of them in the next year. And, while I’m at it, thank you very much to the whole Sharkfest team for running the conference every year!
Also, it was a great idea to have food trucks do the catering for one of the evening events:
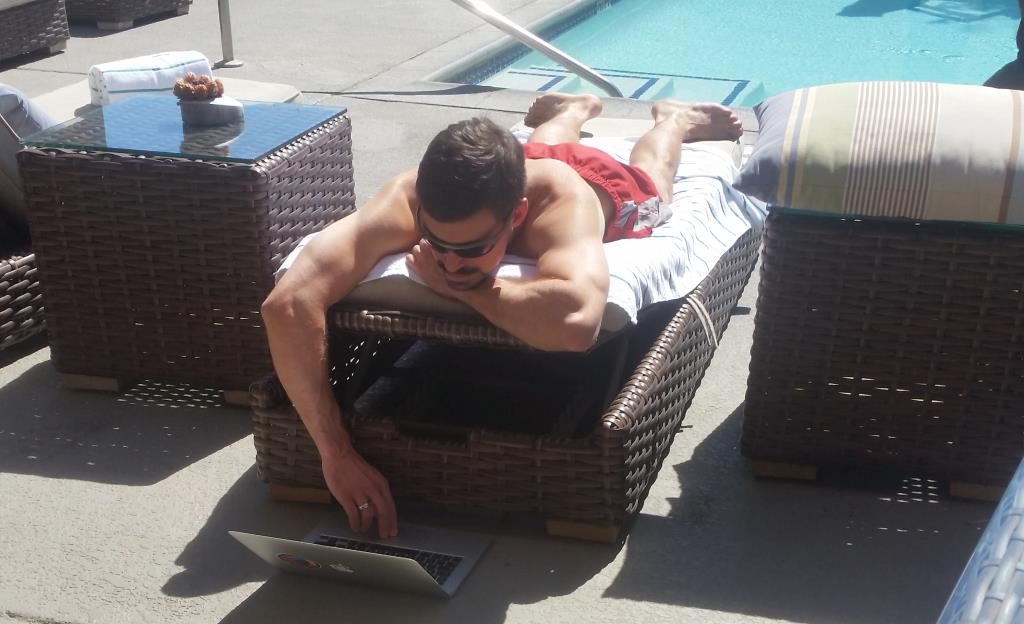
Staying at the same hotel as the Wireshark core developers turned out to be great fun – I think during that week more laptops were present in the pool area than ever before. Of course everybody was at the Computer History Museum during the conference days, but this is what looked like on the weekend before the conference started (also, some presenters creating their slide decks, of course, because they are never final until right before the talk starts, as an unwritten rule 😉 ):
Who’s to say that you can’t look cool while developing Wireshark? 🙂
Final words
For me, Sharkfest 2016 felt extremely short – and most people I talked to felt the same. We were looking at each other like “what, it’s over already?” during the closing reception. I certain that that’s a good sign, because it means that we all had an interesting time, with not a boring minute in sight. I had many good personal conversations with presenters, core developers, attendees and staff, and it wasn’t always about packet analysis either. The Sharkfest crowd is just a bunch of very friendly and curious people, and the attitude of learning and helping each other is awesome. I remember Landi having trouble connecting his laptop to the HDMI splitter for the three HD projectors in the big hall. He needed DisplayPort to HDMI, but everyone we knew only had Mini-DP to HDMI. So he used VGA to put up a note on one of them asking if someone had an adapter for him, and in no time three people showed up to offer theirs – problem solved 🙂
So thanks again to everyone at Sharkfest, and see you next year (or in Arnhem, of course)!






Great recap! Looking forward to visiting Sharkfest Europe lateron this year.
Hope to see you there.
Thank you, I’ll see you there for sure! By the way, this is the first comment posted via IPv6 ever 😉
I was a newbie at Sharkfest this year and it was pretty amazing. I loved that I attended no fewer than 4 sessions with presenters whose blogs/websites/videos I had already read and watched. I think I attended all of your sessions which were great.
It’s a conference like no other and I think it’ll be even better next time now that I know what it’s like (admittedly, I was hesitant to approach presenters with my “real-world” problem b/c I thought it might be annoying). But next time, I’ll get over my introverted self and leverage the smart people that are there.
Thanks, Dori – maybe we should tell people more often that it’s fine to come to us…
I didn’t know you were wanting IPv6 comment’s, hopefully here’s another.
The Developers Den also suffers a little from the “invisible barrier” that folks seem to think exists. The core devs are available there to consult with at most times, just occasionally we shut the door for a meeting when we need to concentrate on the task, but we do try to keep those times to a minimum.
If anyone reading this blog and is able to get to Arnhem in October and hasn’t yet signed up for SharkFest Europe (https://sharkfesteurope.wireshark.org), what’s holding you up?
Yup, I can confirm, IPv6, too 😉
It’s the same problem I discussed with Hansang and Sake – people do not seem to dare to approach us with their analysis problems. So I think we should have an official paragraph in Gerald’s keynote (or welcome speech) explicitly stating that anyone is welcome to talk to any of us. I’ll try to remember to encourage the audience in my talks as well.
Hi Jasper,
If I have a chance I will come by to see hello during the SF16.eu
But I do not have any analysis problems at the moment.
Or rather my biggest issue is getting captures from our customers.
And reproduce the issue.
To analyse the captures is much less an issue.
And yes, I will probably skip your chats as I have seen those online and go for the parallel ones. (Sorry 😉 )
Best regards,
Alcindo
Thanks, come and say hello when you can! And that’s fine, no problem, go see any talk you want 🙂