Sharkfest 2017 EU Recap
In 2017 the Sharkfest Wireshark user and developer conference happened once again in Europe – in the Hotel Palacio Estoril in Portugal, to be more specific.
Sharkfest is a special conference for me, which some of my readers may already know if you read my other recaps – there’s just no other place where you can meet so many other network analysts and geek out about capture files, Wireshark and networking in general. Portugal was an interesting choice for the 2nd european Sharkfest, even though I have to admit that I wasn’t sure about the location at first. It’s pretty much “on the very edge of Europe”, and I wasn’t sure if enough attendees would be willing in traveling the distance to that spot. But they did, and we had over 30 different countries represented. And yes, before you ask – you can attend Sharkfest EU if you’re from all over the world, not just Europe 🙂
I did four talks at Sharkfest EU, with a total of 32 slides combined – so you can imagine they were very non-PowerPointy and quite interactive.
My solo talks
I did a TCP talk for beginners (where, once again, only a couple of attendees had bothered to download the traces beforehand, sigh), and one with more complicated traces. The discussion with the audience was great, and I thank everyone for their feedback afterwards, which really helps all of the presenters to improve our content. Then there was a TraceWrangler presentation which covered the extraction of frames from large sets of file, same as at Sharkfest US. All of my talks were recorded, so you can watch them at the Sharkfest 2017 EU Retrospective page.
Packet Doctors
The last of the four talks were the “Packet Doctors”, with Landi, Sake and me. If you haven’t heard about “Packet Doctors” yet – it’s a 100% interactive session with four experienced packet analysts (Hansang Bae, Sake Blok, Christian Landström and Jasper Bongertz), where the audience hands over their own PCAP files for live analysis. The first time we did this was at Sharkfest US in Pittsburgh, and it was a lot of fun. Unfortunately Hansang wasn’t able to travel to Sharkfest EU (and I am quite sure he still kicks himself for that fact 🙂 ), so we had only three doctors present this time.
Here’s how the “Packet Doctors” session works:
- Attendees bring their real world problem trace files for the doctors to take a look at
- The doctors hadn’t seen any of them before the session starts, so the audience can watch the doctors work their way through unknown packets
- After the talk, all trace files are wiped from the doctor’s laptops again
In both sessions (the one in the US and the one in EU) we were able to pinpoint at least one problem in a trace submitted to us, but I think the most interesting part for the audience is to see that all of the doctors have different approaches to analyzing packets. Sometimes we get ourselves in trouble as well (of course it was me, by not realizing a HTTP cookie was valid for 24 hours and a second, not just 1 second 🙂 ), but that’s how it works.
One final note about “Packet Doctors”: it’s never video recorded, and there will be no download location for the trace files. The reason is pretty simple: the packets we work on are real life, non-anonymized captures in most cases, so we can’t expose them to the public. We also ask the audience to follow the Chatham House Rule for the same reason. To sum it up: be there or be square 😉
Other talks
The standard problem of any Sharkfest is that there are so many talks and you can only watch one at the time. So to all of my presenter friends: if I wasn’t watching your presentation it’s just because I can’t clone myself (which is something my Employer apparently often regrets as well). Also, sometimes it’s simply time to network with others in a non-technical way (the so-called “hallway track”):

Hallway Track: Sake, Peter, Jaap and Anders – notice the Sharkfest EU Portugese mini dictionaries on the table 🙂
Or take a time out (called the “pool track”):
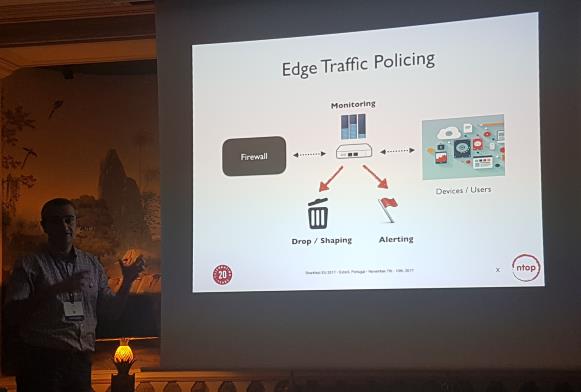
I always try to see talks by presenters I haven’t seen before, and this time I started even before Sharkfest had officially begun, by visiting the ntop User Group Meeting hosted by Luca Deri and his team:
There were multiple presentation on various aspects of Netflow processing and packet capture in general, e.g. on selecting the best hardware for a small remote capture box, e.g. the APU2 platform by PcEngines, which I often use for pfSense firewalls as well.
The ntop guys really contribute a lot to the community, and you should check out their solutions if you’re interested in finding out what your network is doing. It went as far as Luca giving away 6 Napatech 4x1GBit capture cards for free (!!!) to the audience (now I’m sure most of you would have wanted to be there, right? 🙂 ).
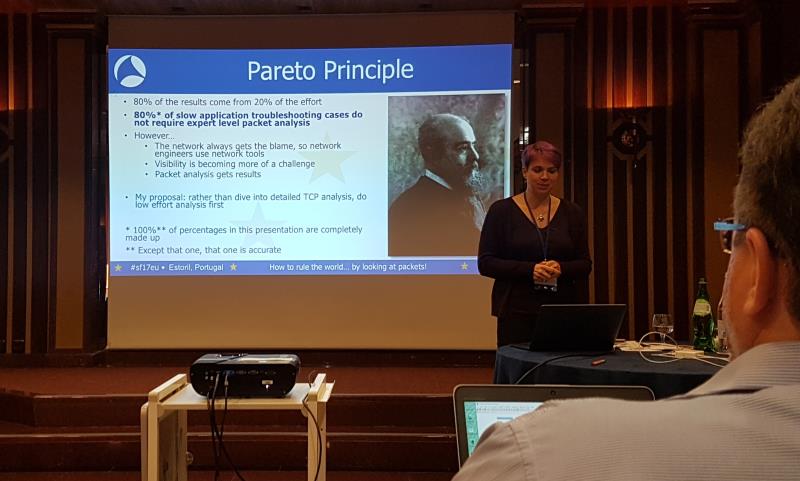
Then there was a talk by Lorna Robertshaw I was quite interested in, because she has a ton of experience in network troubleshooting:
I really liked the talk she gave, once again showing new ways of reaching the goal when looking at packets, and a great sense of humor (I just love the comment at the bottom of her slide in the picture above) – I hope she’ll be back at the next Sharkfest, and I absolutely recommend visiting her talk.
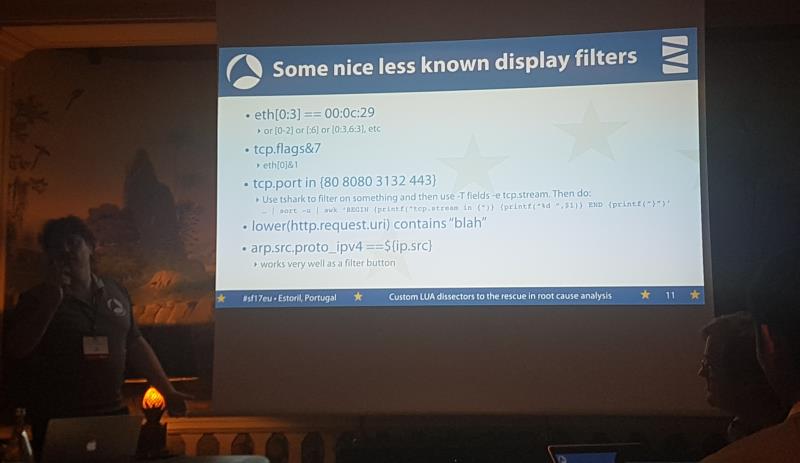
Then there were the Developer Bytes, in which the Wireshark core developers talked about Wireshark internals or other topics they’re working on. The technical level varied quite a lot (I have to admit I was quite lost on Richard’s segment, but I have trouble reading Wireshark code anyway), but there were also bits in the second half that anybody would have found useful, e.g. the SSL decryption part by Peter, or the filter tricks by Sake:
The EsPCAPe room challenge
Like at Sharkfest US, Sake gave us his esPCAPe room challenge in the evening one day, and I have to bow my head in respect to that guy – other than many may have expected he built a completely new challenge for Sharkfest EU, instead of reusing the one from Sharkfest US. Once again it turned out “Wireshark + Jasper + SSL decryption = nope, bro”, but thanks to the rest of the team (including the ntop guys) we made 3rd place anyway! Thanks, team! 🙂
The Location
Palacio Estoril was simply an amazing location. I have to mention the Spa here, which was included in the room fee, and a big thank you to Janice (you know why 😉 ). I think we all loved the warm weather (felt like California, and don’t forget – this was in November, in Europe!). Also, the food way simply amazing (by far the best at any Sharkfest I’ve been to, I think, but that’s personal preference, of course):
Oh, by the way, outside the Hotel, Eddi and I found a “Tech Tree” of a different kind:
Final words
For me, Sharkfest is one of the “recharge events” where I can relax and recover from all the energy draining things at work. Meeting old and new friends, talking about ideas, packets, Wireshark, TraceWrangler, capture hardware (hi to Steven from Endace, Chris from Garland Technology and the guys from ProfiTAP!). Without Sharkfest there would be a lot less happening at this blog, or with TraceWrangler, or at the Wireshark Q&A site…
Oh, and not to forget: Betty brought me Jawesome Shark glasses, too – thank you so much!
At this point I have to thank Gerald and Janice to keep organizing an amazing conference for all of us. Also thanks to Sheri as well for coming back to help Janice – it seemed a much more relaxed experience than some I’ve seen (San Rafael comes to mind) for both of you 😉 And not to forget Angelo, recording hero that makes sure all of you can watch the talks in teh big room!







Discussions — No responses yet